How Serious is CVE-2024-38063? Assessing the Criticality of RCE Vulnerability on Windows Systems with IPv6

The discovery of CVE-2024-38063, a critical Remote Code Execution (RCE) vulnerability affecting Windows systems with IPv6 enabled, has raised concerns across the cybersecurity landscape. While the severity of this vulnerability is evident, the actual level of risk it poses to your organization depends on several factors, including your network configuration and security practices.
Understanding CVE-2024-38063: A Quick Overview
CVE-2024-38063 is part of the August 2024 Patch Tuesday release and affects Windows systems with IPv6 enabled. This vulnerability allows an attacker to execute remote code on a vulnerable machine, which could lead to unauthorized access or further exploitation. However, the likelihood of an attack succeeding depends on how IPv6 is configured in your network.
Daily Scans and Security Posture: A Proactive Approach
Assessing your current security posture is one of the first steps in determining your exposure to CVE-2024-38063. Regular perimeter scans are essential in identifying vulnerabilities as they emerge. This is a positive sign if your organization conducts daily scans and hasn’t been flagged as vulnerable. However, it’s important not to become complacent—ongoing vigilance is critical to maintaining security.
IPv6 in Your Environment: Should You Be Worried?
IPv6 is a common feature in modern network environments, often enabled by default on many systems. However, its mere presence doesn’t necessarily make your organization vulnerable to CVE-2024-38063. The actual risk depends on how IPv6 is used within your infrastructure.
IPv6 may be enabled but not actively used for critical or external-facing functions for many companies. If this is the case in your environment, the potential for exploitation is significantly reduced. Confirming this through thorough network documentation and consultation with your network team can provide additional peace of mind.
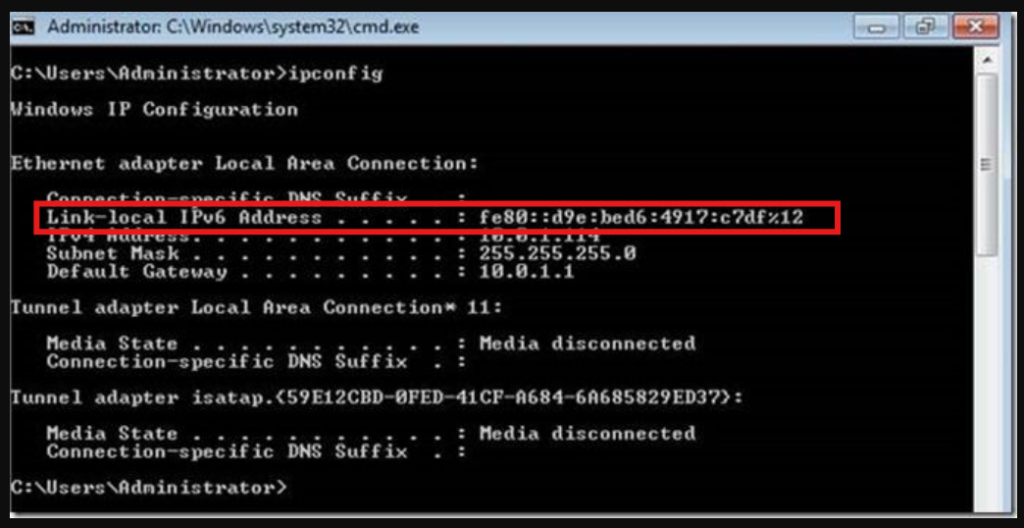
It’s also important to understand that not all IPv6 addresses are equally vulnerable. Specifically, link-local IPv6 addresses, which are typically not routable beyond the local network segment, pose a lower risk.
Link-Local IPv6 Addresses: A Limited Threat
Link-local IPv6 addresses (e.g., those starting with “FE80”) are not routable, meaning they cannot be used to move laterally across your network. Routers do not forward packets with link-local source or destination addresses, limiting the potential for an attacker to exploit CVE-2024-38063 in a meaningful way. The only scenario in which this vulnerability could be exploited is if an attacker has already gained access to a machine and is trying to execute code on that same machine—a situation that, while serious, does not allow for broader network compromise.
Patching and Mitigation: Stay Ahead of the Threat
A fix for CVE-2024-38063 is available as part of the August 2024 Patch Tuesday update. While this vulnerability may not present an immediate threat in your environment due to the specific nature of your IPv6 configuration, applying patches as soon as they are released is still critical. This ensures that your systems remain secure against both known and emerging threats.
Even if the vulnerability cannot be easily exploited in your current setup, keeping your systems up to date is a best practice that protects against future risks. Regular patching and ongoing network assessments can help maintain a strong security posture.
Conclusion: A Measured Response to CVE-2024-38063
CVE-2024-38063 is a severe vulnerability that warrants attention, but the actual risk it poses to your organization depends on your specific network configuration and security practices. For many companies, the presence of IPv6 does not automatically translate into heightened vulnerability, mainly if link-local addresses are used, and the protocol is not a critical part of the external-facing infrastructure.
By maintaining regular security scans, verifying your network documentation, and applying patches in a timely manner, you can mitigate the risks associated with CVE-2024-38063 and keep your systems secure. Stay informed, stay vigilant, and continue to prioritize proactive security measures to protect your organization from potential threats.